Dark endpoints: an invisible threat to your IT team

Invisible devices create significant blind spots that can leave IT departments helpless to act against a breach until it is already too late. A new report from Absolute found 13% of enterprise devices aren't connected to the corporate domain.
The Absolute platform delivers self-healing endpoint security and always-connected IT asset management to protect devices, data, applications and users — on and off the network.
Unmasking the Invisible Threat: Your Guide to Network Security
EDR Endpoint Vulnerabilities Are Disastrous

Why You Need to Accelerate 'Time to Compliance
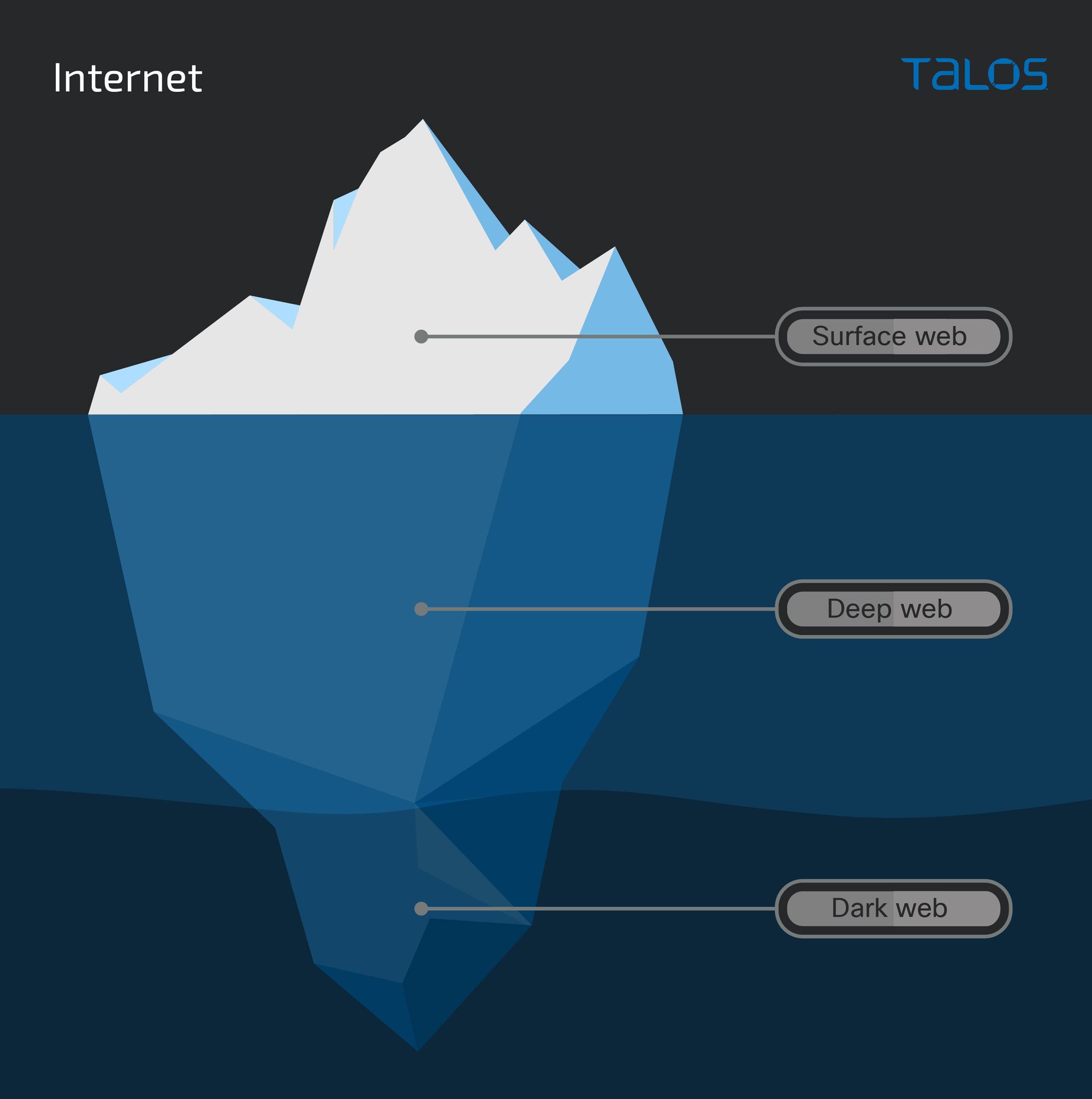
What is the dark web?

Blog, Author, Michelle Base-Bursey
What Is Endpoint Detection And Response? (And Why It's Important)

The Invisible Threat: Building Cyber Resilience to Respond to the

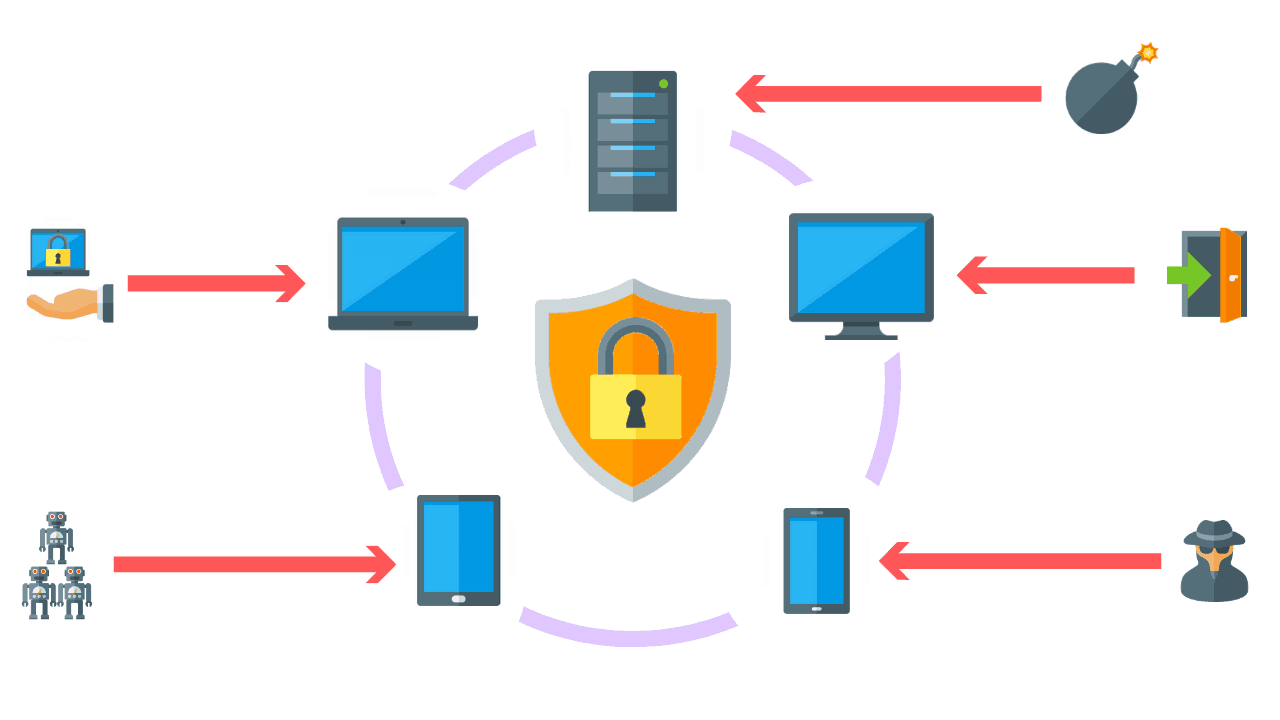
The Internet of Things: Risks & Mitigation Strategies

Top 10 Endpoint Detection and Response Tools in 2022 - Spiceworks
Zero-Day Vulnerabilities - The Invisible Threat - Patch My PC
Responding to Multi-Endpoint Threats with XDR

The Rise of Endpoint Security Risks: 6 Common Types

Unweaving A Complex Web of Threats

Forescout Technologies Inc.